New Cybersecurity Threat: Phone Cables
Cyberattacks have become increasingly complex over the years and unfortunately, a lot of them are undetectable by the average person. Below, Cody Bedford, a Technical Account Manager for Kavaliro's Managed IT Services division, shares his insight on a new way that cyberhackers can get to you, through your phone cable.
As someone with an IT background and a specialization in cyber security, I feel compelled to share a recent revelation that has left me and many others in the cybersecurity community astonished. We're all aware of the risks associated with inserting flash drives into unfamiliar or untrusted computers. However, cyber security threats have now evolved to target something as seemingly innocuous as phone cables.
Yes, you read that right – phone cables. I'm not referring to a cable connected to a phone, but the cable itself.
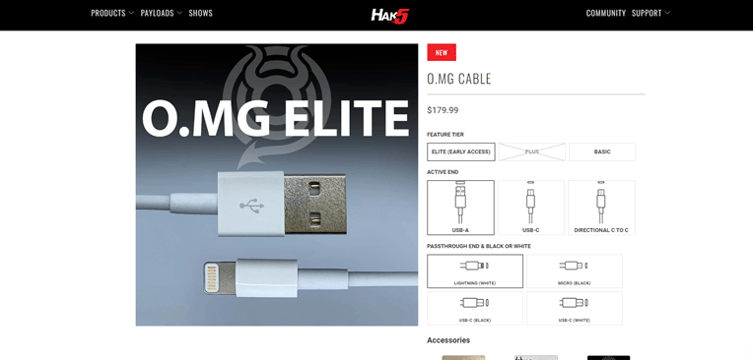
In the product image above, you can see what appears to be an ordinary iPhone cable. However, hidden within the USB plug's square, metal shield, is a microcomputer with Wi-Fi access. This tiny device can run scripts and keyloggers to track users' keystrokes, posing a significant security risk. I have actually ordered one of these deceptive gadgets to test its capabilities and determine the potential dangers, such as the limits of its Wi-Fi access.
Fortunately, these cables are just beginning to appear on the market and aren't yet mainstream. As we and other organizations conduct tests, these devices should become easier to detect.
Nonetheless, it's crucial to exercise caution when encountering free cables or those found lying around. Most importantly, never plug your phone directly into your computer to charge it.
Remember, cyber security attacks are 99.99% preventable, often resulting from end users performing seemingly harmless actions (like plugging a phone into a computer) without considering the potential consequences. By staying informed about the latest tactics used by cybercriminals, we can work together to keep our data safe!
Contact us today at kdrinan@kavaliro.com to learn more about our managed IT services and discover how we can help you fortify your business against the ever-evolving landscape of cyber threats.
Written by Cody Bedbord, Technical Account Manager - Kavaliro MSP


